A Risk Management Framework for Enterprise Endpoints & Remote Workers
by Tyler Rohrer on October 24, 2022
Half a billion of our team members really wanted to work remotely. Overnight, they all got their wish. While most of the chatter is and was around the end user, system administrators and security professionals were the essential front-line workers and first responders. You kept the lights on.
Collaboration across technology domains got more difficult, security requirements and costs spiked, and we lost control of a ton of previously managed infrastructure. Work and workers happened anyplace, at anytime, on any network. Risk increased.
When it comes to those end users...we really don’t think they are coming back. This major shift to remote work creates new friction points in support and systems management, it also explodes our possible attack vectors. Many of our legacy tools, systems, and run books are suddenly outdated.
Interestingly some of the first markets to adjust to this new work from anywhere model were the Cyber Insurance and Risk Insurance Carriers. They realized that 500,000,000 new people on untrusted networks, in difficult to manage locations, with local admin rights was going to be a nightmare. Premiums adjusted instantly to reflect this new risk posed to the organization, and the probability, pervasiveness, and severity of possible breaches and cyber incidents. These new risks are real.
While the past few years have seen most organizations in “survival mode” when it comes to end user computing, operating on a theory of best effort, the financial, technical, and productivity risks we now face compel us to engage in “real effort”.
.png?width=311&height=162&name=download%20(1).png) Having a cohesive Risk Management Framework can be essential to lowering the risk and exposure your remote and distributed team members pose to themselves and the organization.
Having a cohesive Risk Management Framework can be essential to lowering the risk and exposure your remote and distributed team members pose to themselves and the organization.
While the US Department of Defense, together with NIST (National Standards in Science & Technology) have developed an RMF Process for modern organizations – little work has been to date to extend this to remote users, endpoints, or in the domain of end user computing. Simply stated a Risk Management / Mitigation Framework is a lifecycle you adopt to become continuously aware, and able to repel – cyber risk.
In the context of the 5 steps of RMF – we can apply each one to our new “work from anywhere” use cases. In fact, what we often find is not just higher fidelity to security and compliance standards, but also opportunities to optimize infrastructure, applications, and processes.
Identify the Risk In the domain of end user computing - conducting a comprehensive Assessment is an excellent way to identify risks you may face at the edge, or with the applications, identity, or data in the cloud. Device, identity, application, and data security can all be measured. This together with endpoint and end user information adds dimensionality to our assessment.
In the domain of end user computing - conducting a comprehensive assessment identifies the risks you may face at the edge, or with the applications, identity, or data in the cloud.
 Analyze the Risk With this information, we can then begin to analyze both the patterns we see across our distributed workforce, but also areas for increased enforcement or policy / process creation. Are the defenses we deploy, compliance measures we put in place, and security frameworks we designed working? Are users working around or breaking the software, systems, and policies we are asking of them? Perhaps, there are opportunities to improve or optimize system or technology choices we have already made, or are about to make.
Analyze the Risk With this information, we can then begin to analyze both the patterns we see across our distributed workforce, but also areas for increased enforcement or policy / process creation. Are the defenses we deploy, compliance measures we put in place, and security frameworks we designed working? Are users working around or breaking the software, systems, and policies we are asking of them? Perhaps, there are opportunities to improve or optimize system or technology choices we have already made, or are about to make.
Prioritize the Risk With a full spectrum of data from across our organizations looking at the edge to the cloud and back – we can plan. Should we see pockets of risk, voids in coverage, or mistakes in process - we can then begin to prioritize which teams and tasks to delve into first, and with what resources. Large or distributed teams can make completing these tasks time consuming and expensive. Unifying consoles in mandatory for full data clarity and use.
Address the Risk Next we need to address the risk – we endeavor to fix stuff, isolate, quarantine, eliminate, as the use case demands. This is where we have the most tactical opportunity to effect change. New systems, applications, architectures, policies, or compliance standards and processes we put in place. The goal is typically similar – productivity of our staff, our budget, and our end users. We want to insure that our security posture is maximized while our exposure to risk is minimized.
Monitor the Risk Finally, we must realize that no environment is static and the moment we effect change our solutions will begin to drift. Continuous monitoring and observability ensure that the introduction of new risk can be seen and responded to left of boom. Updating, patching, remote user behavior, contextual security information on vulnerabilities and networks can have zero-day impact in terms of how we can protect our organizations. 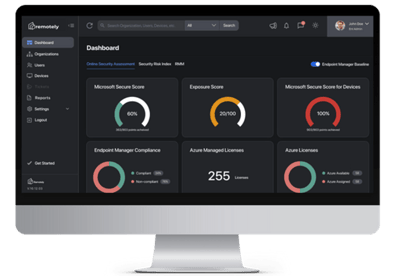
While the productivity debates surrounding work from anywhere strategies will take years to settle, what is incontrovertible is that distributed teams present more risk. Having a logical Risk Management Framework for your end user computing and endpoints can save teams tremendous time in shifting from tactical / response-based management to strategic, value-added processes.
At Remotely, we are proud to have built a frictionless, cloud native unified console that allows system administrators and security practitioners eager to begin a Risk Management Framework. See, secure, and support your end users like never before, while delivering amazing outcomes for the business.
T.Rex
Click below for a Demo
Enterprise Risk Management Framework Demo
Add some fun, compelling content here
- Cyber Security (16)
- Security (15)
- Azure (10)
- Cyberattack (10)
- IT Operations Management (10)
- Remote Monitoring and Management (10)
- AIP (9)
- IT Strategy (9)
- Remote Work (9)
- Asset Management (7)
- IT Operations (6)
- Asset Inventory (5)
- Reliability (5)
- Remotely Interesting (5)
- Risk Management Framework (5)
- Azure Migration (4)
- Microsoft Secure Score (4)
- Office 365 (4)
- Security Risk Index (4)
- Customer Success (3)
- GRC (3)
- Risk Dashboard (3)
- Support (3)
- Powershell (2)
- First Steps (1)
- Migrate (1)
- System Requirements (1)
- Virtual Machine (1)
- Zero Trust (1)
- August 1, 2023 (1)
- July 1, 2023 (2)
- May 1, 2023 (1)
- March 1, 2023 (2)
- February 1, 2023 (1)
- January 1, 2023 (1)
- December 1, 2022 (2)
- November 1, 2022 (2)
- October 1, 2022 (1)
- September 1, 2022 (2)
- August 1, 2022 (1)
- July 1, 2022 (1)
- June 1, 2022 (2)
- May 1, 2022 (4)
- April 1, 2022 (3)
- March 1, 2022 (2)
- February 1, 2022 (2)
- January 1, 2022 (1)
- December 1, 2021 (4)
- November 1, 2021 (1)
- October 1, 2021 (1)
.png?width=50&height=50&name=Untitled%20(50%20%C3%97%2050%20px).png)


No Comments Yet
Let us know what you think